Simple way to generate a Subject Alternate Name (SAN) certificate
What will I cover in this post?
We will learn how to generate the Subject Alternate Name (or SAN) certificate in a simple way.
In this post, I plan on:
- Explaining what is the SAN certificate
- Explaining how to create the SAN certificate using the Java keytool
- Explaining how to export the certificate private and public keys using OpenSSL
- Explaining how to create the Certificate Signing Request (CSR) for the SAN certificate using the Java keytool
Do not forget to follow me on Twitter
What is the SAN certificate?
The Subject Alternative Name (SAN) is an extension the X.509 specification. The specification allows to specify additional values for a SSL certificate. These values added to a SSL certificate via the subjectAltName field. A SSL certificate with SAN values usually called the SAN certificate.
Why to use the SAN certificate?
RFC 2818 recommends to use the SAN certificate instead of a regular SSL certificate :
Although the use of the Common Name is existing practice, it is deprecated and Certification Authorities are encouraged to use the dNSName instead.
What are the supported values?
The full list of supported values listed in RFC 5280.
Recommended to configure the following values (where applicable):
- a DNS name
- an IP address
- an Internet mail address
How to create the SAN certificate?
The command below will create a pkcs12 Java keystore server.jks with a self-signed SSL certificate:
keytool \
-keystore server.jks -storepass protected -deststoretype pkcs12 \
-genkeypair -keyalg RSA -validity 365 \
-dname "CN=10.100.0.1," \
-ext "SAN=IP:10.100.0.1"
The command below will list certificates in the keystore:
keytool -list -v -keystore server.jks -storepass protected
The snippet below shows the partial output only with the Subject (Owner below) and SubjectAltName (SubjectAlternativeName below) fields:
...
Owner: CN=10.100.0.1
...
Extensions:
#1: ObjectId: 2.5.29.17 Criticality=false
SubjectAlternativeName [
IPAddress: 10.100.0.1
]
The certificate in a browser
Configure your webserver to use the certificate and you will be able to check the certificate in a browser.
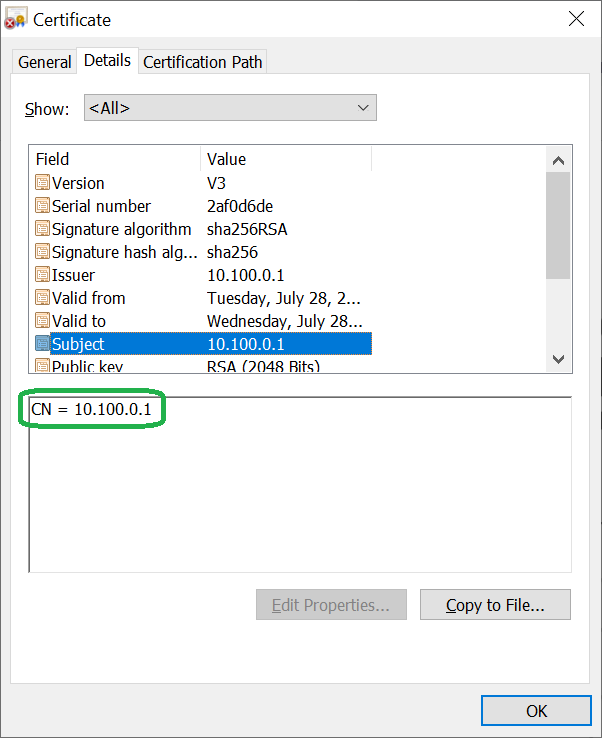
The Subject field:
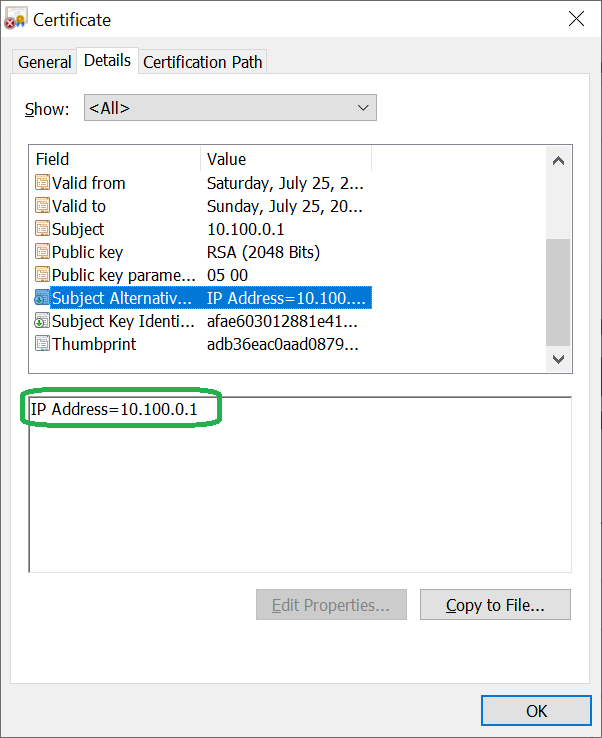
The SubjectAltName field:
Export the certificate private and public keys
The Java keytool does not support export of a private key therefore we will need to use OpenSSL.
The command below export the private key to the file serverkey.pem:
openssl pkcs12 -in server.jks -nodes -nocerts -out serverkey.pem
You will need to provide the keystore password (protected).
Enter Import Password:
MAC verified OK
The command below export the public key to the file servercert.pem:
openssl pkcs12 -in server.jks -nokeys -out servercert.pem
You will need to provide the keystore password (protected).
Enter Import Password:
MAC verified OK
How to create the CSR for the SAN certificate
Create the SAN certificate
First create the SAN certificate with all values:
keytool \
-keystore server.jks -storepass protected -deststoretype pkcs12 \
-genkeypair -keyalg RSA -validity 395 -keysize 2048 -sigalg SHA256withRSA \
-dname "CN=myserver.mydomain.com,O=myorganization,OU=myou,L=mylocation,ST=California,C=US" \
-ext "SAN=IP:10.100.0.1,IP:192.168.0.1,DNS:myserver.mydomain.com,DNS:otherserver.otherdomain.com,EMAIL:[email protected],EMAIL:[email protected]"
The command requires the following values for the Subject field:
- CN - Common Name
- O - Organization
- OU - Organizational Unit
- L - City or Locality
- ST - State or Province
- C - The two-letter country code
The command requires the following values for the SubjectAltName field (where applicable):
- IP - List of IP addresses of your server
- DNS - List of DNS names of your server
- EMAIL - List of emails
The certificate in a browser
The Subject field with all values:

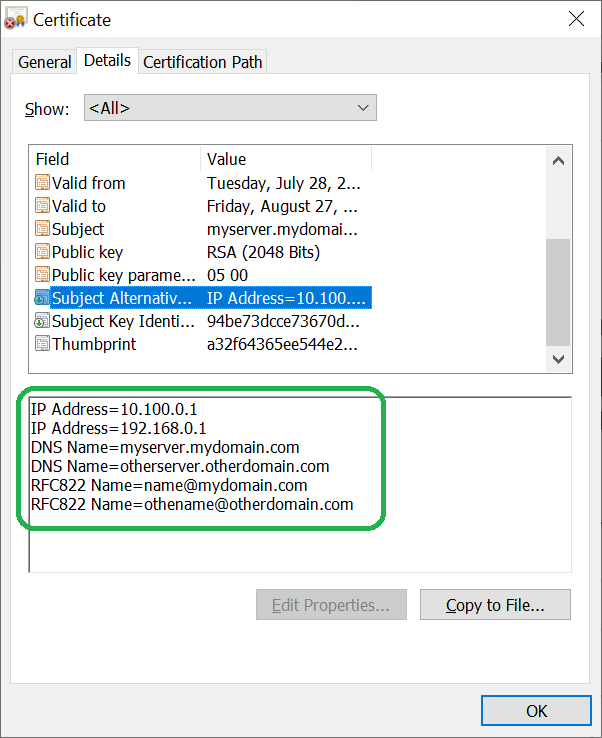
The SubjectAltName field with all values:
Export CSR using the Java keytool
The command below will export the Certificate Signing Request (CSR) into myserver.csr file.
You are welcomed to send the CSR to your favorite CA.
Note: copy the -ext parameter value from the command that creates the SAN certificate.
keytool \
-certreq -keystore server.jks -storepass protected \
-ext "SAN=IP:10.100.0.1,IP:192.168.0.1,DNS:myserver.mydomain.com,DNS:otherserver.otherdomain.com,EMAIL:[email protected],EMAIL:[email protected]" \
-file myserver.csr
Take-aways
You should now have a better knowledge of what is SAN certificate and how to create SAN CSR
