What will I cover in this post?
We will learn how to configure Two-Factor authentication in Keycloak
In this post, I plan on:
- Explaining what is Two-Factor Authentication
- Explaining what is Keycloak Two-Factor Authentication
- Explaining how to configure Two-factor authentication in Keycloak
Do not forget to follow me on Twitter
What is Two-Factor Authentication?
According to wikipedia:
Two-factor authentication (also known as 2FA) is a method of confirming a user’s claimed identity by utilizing a combination of two different factors:
- Something they know
- Something they have or something they are
Keycloak Two-Factor Authentication
Keycloak authenticates users using:
- Password
- An one-time password (OTP)
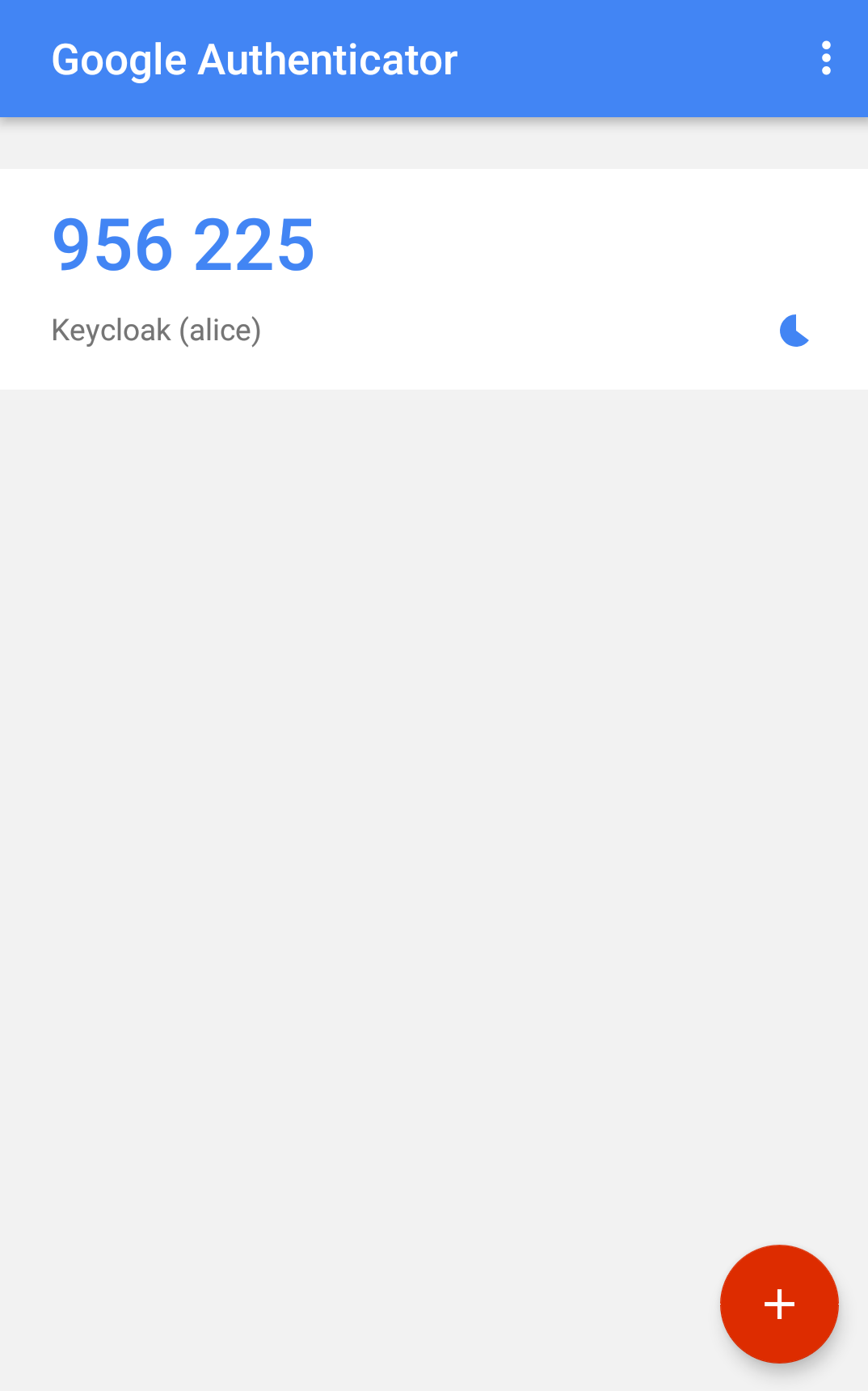
A one-time password generated by Google Authenticator or FreeOTP
Keycloak configuration
Enforce new users to configure OTP
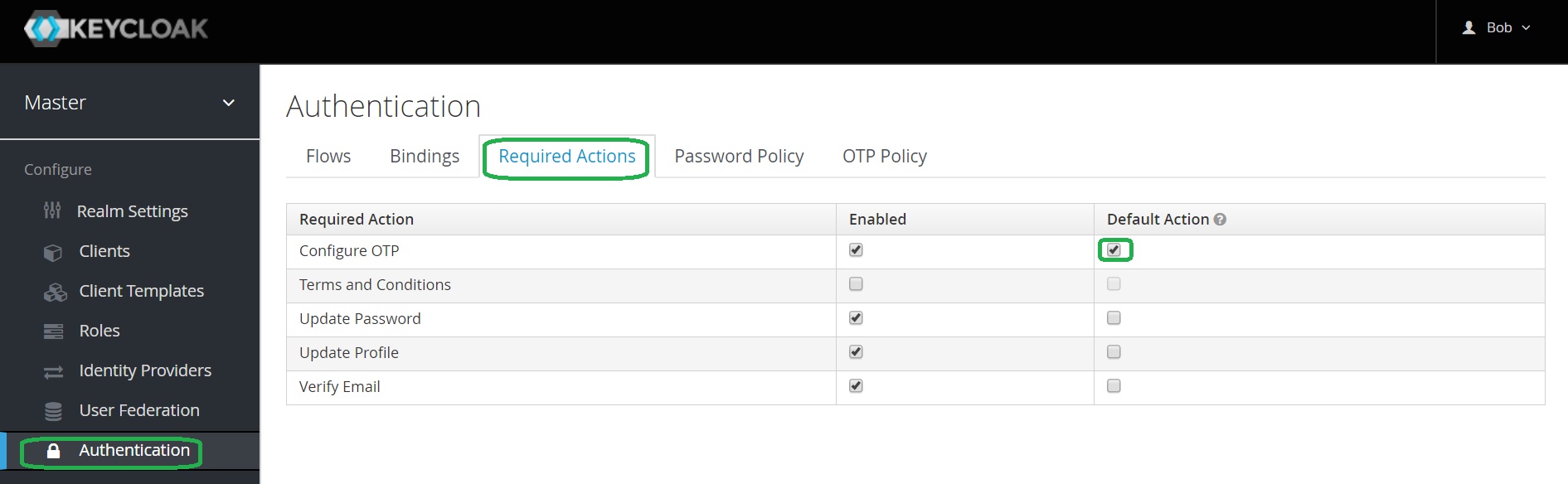
Open Keycloak admin page, open Authentication, go to the Required Actions tab.
Click on the Default Action in the Configure OTP row.
Enforce an existing user to configure OTP
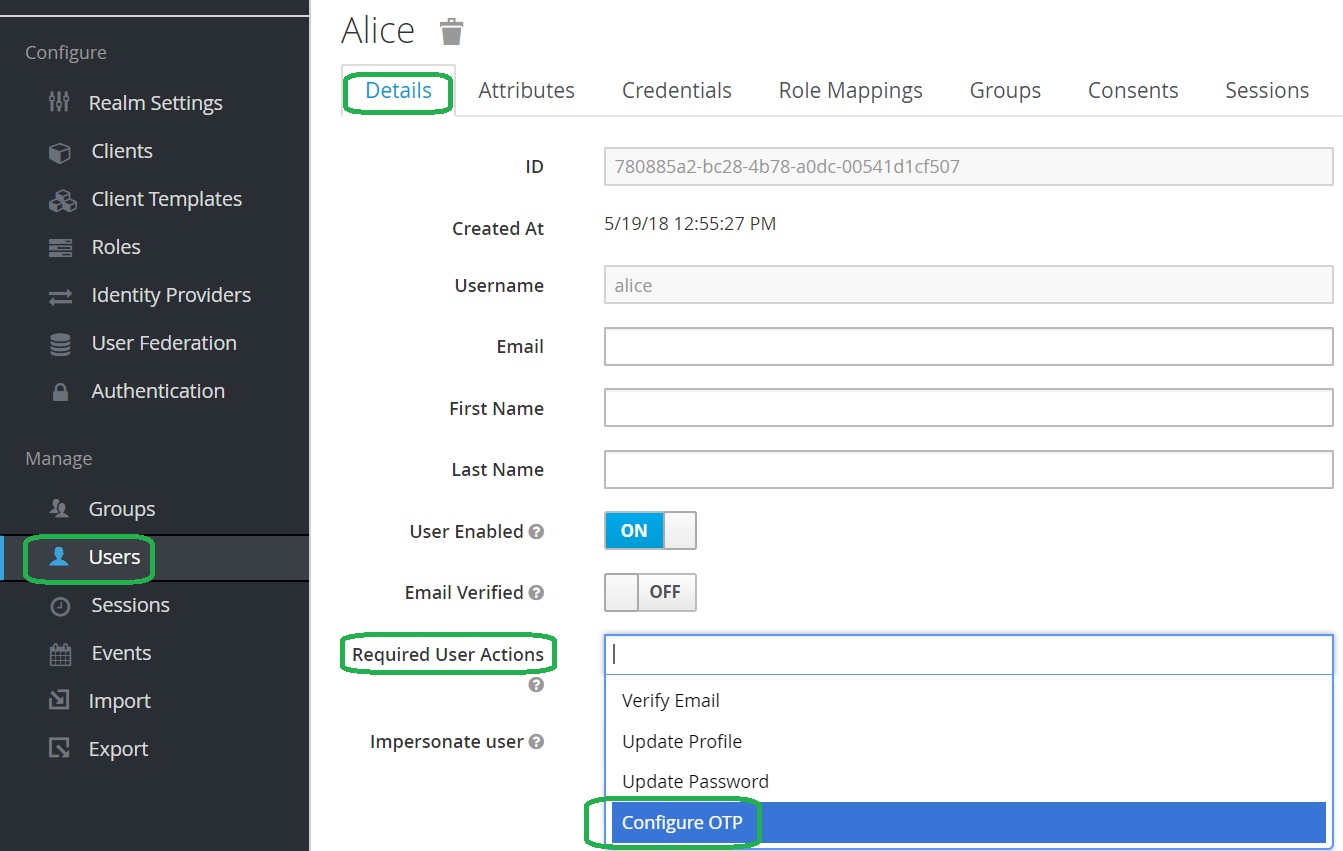
Open Keycloak admin page, open Users, select a user, go to the Details tab.
In the Required User Actions list select Configure OTP.
OTP Policy configuration
Open Keycloak admin page, open Authentication, go to the OTP Policy tab.
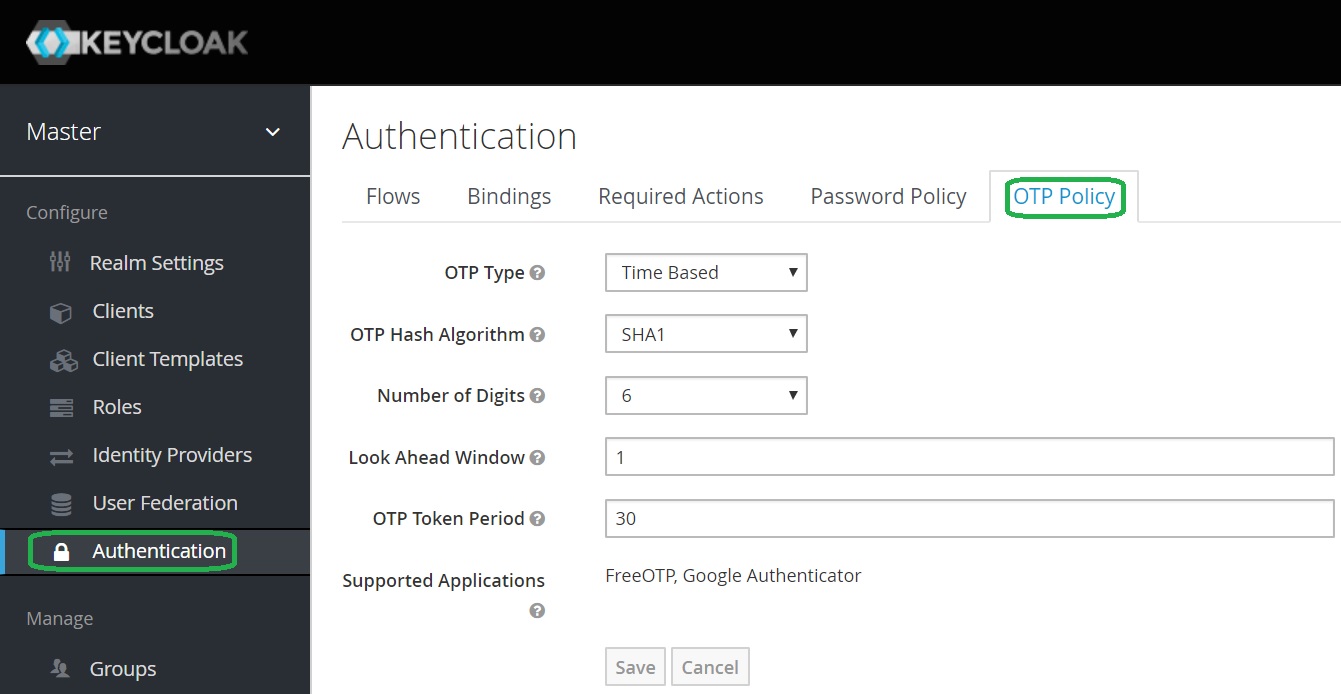
Keycloak documentation related to OTP Policies is here
Recommended OTP Policy
Time based OTP Type (TOTP) is considered a more secure. TOTP requires time be synchronized between Keycloak server and an end user device.
If the server and the device cannot be synchronized use Counter Based type (HOTP).
Configure Look Ahead Window to 3.
User’s Mobile Authenticator
One Time Setup
A user will need to setup Mobile Authenticator upon the completion of the user name password authentication:
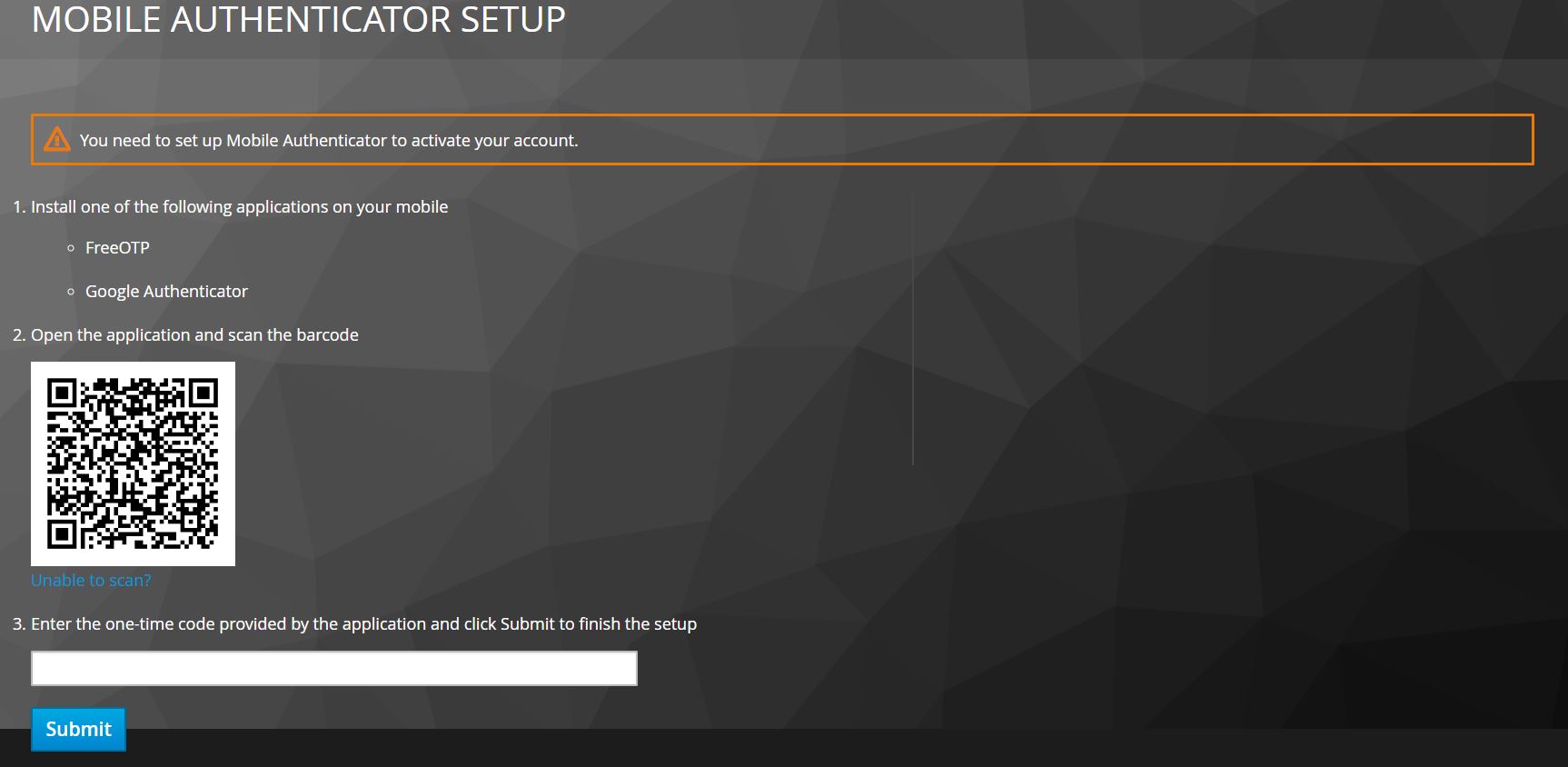
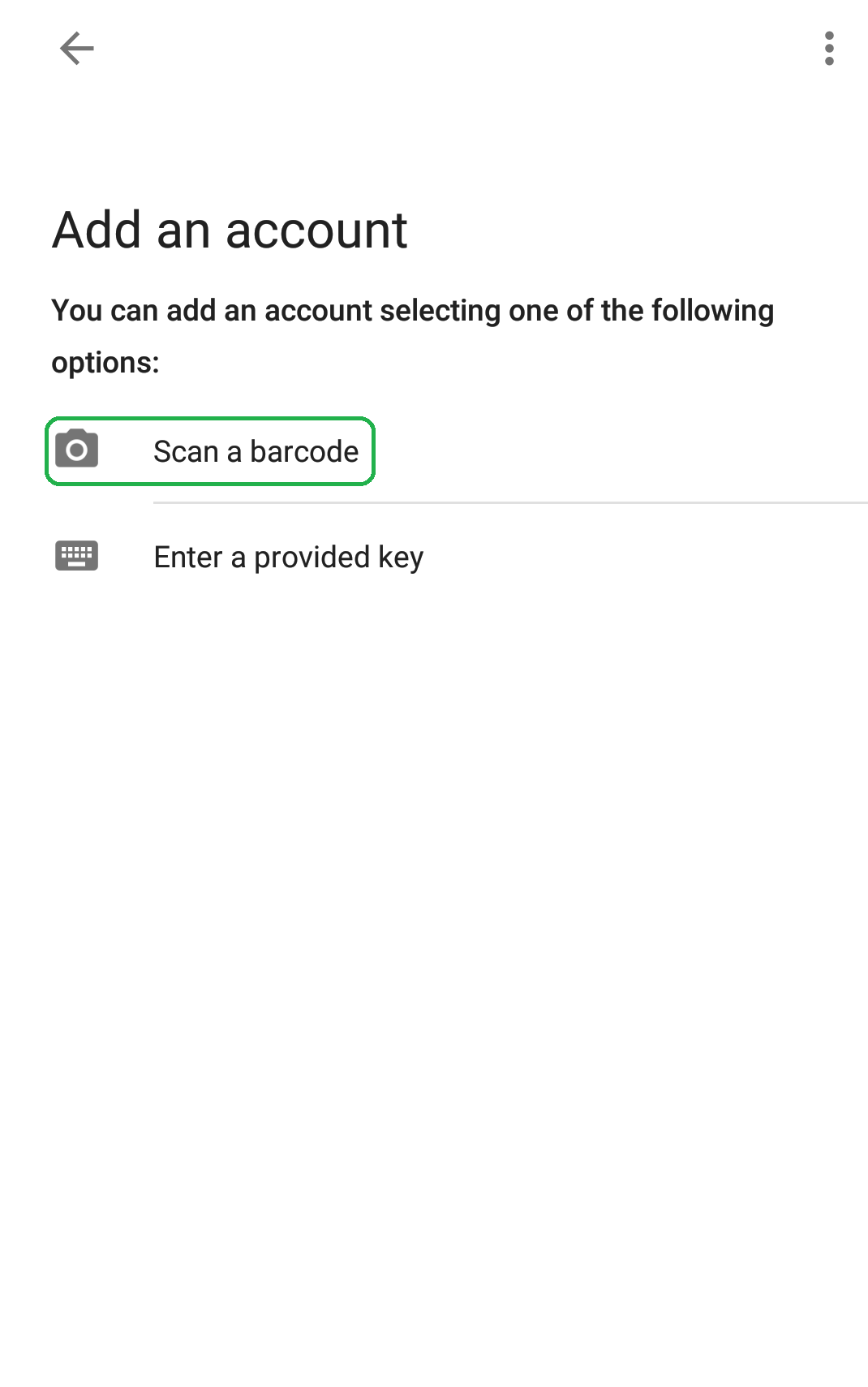
The example below shows the Google Authenticator.
Download
Download Google Authenticator.
Install Google Authenticator
Scan the QR code
Provide the generated code to the Keycloak setup login page
One Time Setup Video
You can watch the example of the registration in the video:
Authentication using One-time code
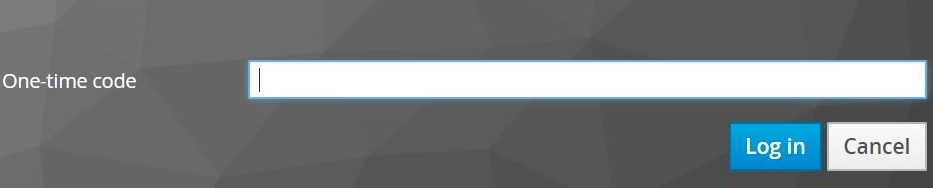
A user will need to provide One-time code upon the completion of the user name password authentication:
Authentication Video
You can watch the example of the authentication in the video:
Take-aways
You should now how to configure Two-factor authentication in Keycloak
